Oracle Cloud Breach: OAM Exploit & T3 Protocol Clarified

Introduction
Over the past few days, we have been in direct contact with a hacker who goes by the alias Rose87168. He claims to have breached Oracle Cloud systems, specifically targeting Oracle WebLogic and Oracle Access Manager (OAM). The hacker has provided us with multiple files and data samples, including a tree file and a 10,000-line dataset, which allegedly contain sensitive configuration files, user authentication data, and directory structures from Oracle's infrastructure.
The hacker stated that they have proof for Oracle, including videos, data, CMS files, and databases. They might also have other sensitive documents and access logs that could be crucial for the investigation.

Adding to the tension, the hacker has posted on Twitter, saying:

"Still, what is it? Does Oracle Cloud still not want to accept what happened? No problem. Let's have some fun."
This blog will detail what was shared, what was found, and the potential risks involved
Data Shared by the Hacker
The hacker has provided several key files and data samples, including:
1. Tree file:

A directory structure dumps what appears to be an Oracle WebLogic or Oracle Identity Management (IDM) server. Files include:
- backup-config.xml – Possible system backup configuration.
- config.xml – May contain critical system settings, including hardcoded credentials or access configurations.
- System Logs – Could provide insights into system activity, errors, or unauthorized access attempts.
2. 10,000-Line Dataset
The dataset appears to contain:
- User-related information, including email addresses and possible hashed credentials.
- Several "null" entries, suggesting incomplete or filtered data.
- Potential identity and access management details from an Oracle Cloud system.
Leaked LDAP Entry (Shared Recently on the Dark Web)
The hacker has now leaked LDAP (Lightweight Directory Access Protocol) entries for a user in an Oracle Cloud-based identity management system. Key details from the leaked data include:
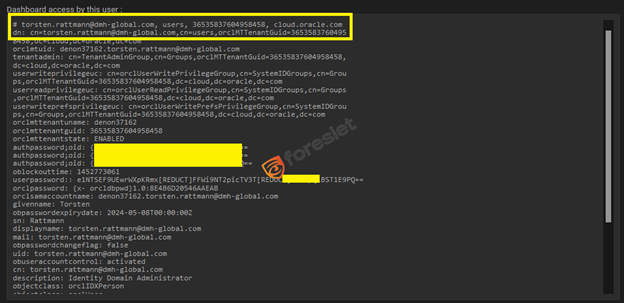
Torsten Rattmann, identified by the email torsten(.)rattmann@dmh-global(.)com, is an Identity Domain Administrator within Oracle Cloud. As a member of the TenantAdminGroup, he holds administrative access, along with write and read privileges on user data (orclUserWritePrivilegeGroup, orclUserReadPrivilegeGroup) and the ability to modify user preferences (orclUserWritePrefsPrivilegeGroup).
His Oracle Cloud tenant, uniquely identified by orclmttenantguid, is currently enabled, indicating an active status. Authentication details reveal that his account uses password hashes (SASL/MD5) stored under authpassword;oid and userpassword, with the password set to expire on May 8, 2024 (obpasswordexpirydate). His account status (obuseraccountcontrol) is marked as activated, and no failed login attempts (oblogintrycount) have been recorded.
Clarifying T3 Protocol and the Exploitation Path
Understanding T3 Protocol in WebLogic Attacks
T3 is a proprietary Oracle WebLogic protocol used for communication between clients and WebLogic servers. Several WebLogic vulnerabilities, such as CVE-2023-21839 and CVE-2023-21931, require T3 access for remote code execution (RCE). Exploiting these flaws typically demands that an attacker can send T3 requests, a process that is often restricted through network segmentation and security controls.Why T3 Was Not Involved in This Breach
The hacker explicitly stated:

"CVE you send need T3 access! OAM RCE used only."
This suggests that T3 access was not required in this attack. Instead, the hacker exploited a known Oracle Access Manager (OAM) vulnerability, likely CVE-2021-35587, which allows unauthenticated remote code execution via HTTP, not T3.
Key differences:
- WebLogic RCE via T3 requires access to the internal network or an exposed T3 service.
- OAM RCE (CVE-2021-35587) can be exploited remotely through an unauthenticatedHTTP request, making it easier to target exposed Oracle Access Manager instances.
By bypassing T3-based WebLogic exploits, the attacker focused on identity and authentication systems, leading to a high-level compromise of Oracle Cloud.
Exploitation Path: CVE-2021-35587
- Allows an unauthenticated attacker with network access to arbitrary code within Oracle Access Manager.
- Grants access to authentication tokens, session credentials, and administrative privileges.
- The hacker obtained Java KeyStore (JKS) files, encrypted SSO/LDAP passwords, and key files, confirming deep access to authentication secrets.
Impact of the Breach
- Compromised Identity Management Systems: Unauthorized access to SSO credentials, LDAP configurations, and authentication tokens.
- Leaked Security Assets: Java KeyStore (JKS) files, encrypted passwords, and Enterprise Manager JPS keys.
- Privileged Access to Oracle Cloud: If the TenantAdminGroup account was compromised, full control over an Oracle Cloud tenant could be possible.
- Potential Ransom Demands: The hacker appears to be extorting organizations for data removal.
Mitigation & Recommendations
1. Immediate Security Measures
- Patch OAM and WebLogic Servers: Ensure that all patches for Oracle Access Manager (CVE-2021-35587) and WebLogic RCE vulnerabilities (CVE-2023-21839, CVE-2023-21931) are applied.
- Monitor Authentication Logs: Check for unusual access patterns, T3 connection attempts, and OAM activity.
- Disable Unused Protocols: If T3 access is not required, disable it to mitigate potential attack vectors.
2. Credential Security
- Reset Admin and Tenant Credentials: Any suspected compromised TenantAdminGroup accounts should have their credentials rotated.
- Enforce Multi-Factor Authentication (MFA): Especially for identity domain administrators and cloud admin users.
- Audit LDAP and Identity Management Settings: Ensure that no unauthorized changes have been made.
3. Threat Intelligence & Monitoring
Organizations affected by the Oracle Access Manager (OAM) breach should take immediate action to mitigate risks and prevent further damage. Tracking leaked data on dark web forums is crucial, as attackers may attempt to sell or distribute stolen credentials, Java KeyStore (JKS) files, and other sensitive information. Continuous monitoring of underground marketplaces and hacker forums can help detect new leaks and potential threat actors involved.
In addition, engaging incident response teams is essential. Organizations should collaborate with Oracle Security Teams and cybersecurity experts to analyze the breach, assess the extent of exposure, and implement containment measures.
This may include forensic analysis, threat intelligence gathering, and patching vulnerable systems to prevent future exploitation.
Lastly, preparing for disclosure is a critical step if customer or employee data has been compromised. Companies should activate a breach notification plan, ensuring compliance with data protection regulations such as GDPR or CCPA. Transparent communication with affected parties can help mitigate reputational damage and provide guidance on securing their accounts.
Conclusion
This breach highlights the ongoing risks associated with unpatched Oracle Access Manager and WebLogic vulnerabilities. The hacker's claims, leaked LDAP entries, and data samples suggest that identity and authentication systems within Oracle Cloud may have been compromised. Organizations using Oracle Identity Management, WebLogic, or Access Manager should take immediate security measures to prevent unauthorized access.
We will continue monitoring the situation for further developments.
About us!
Foresiet is the pioneering force in digital security solutions, offering the first integrated Digital Risk Protection SaaS platform. With 24x7x365 dark web monitoring and proactive threat intelligence, Foresiet safeguards against data breaches and intellectual property theft. Our robust suite includes brand protection, takedown services, and supply chain assessment, enhancing your organization's defense mechanisms. Attack surface management is a key component of our approach, ensuring comprehensive protection across all vulnerable points. Compliance is assured through adherence to ISO27001, NIST, GDPR, PCI, SOX, HIPAA, SAMA, CITC, and Third Party regulations. Additionally, our advanced antiphishing shield provides unparalleled protection against malicious emails. Trust Foresiet to empower your organization to navigate the digital landscape securely and confidently.
Protect your brand, reputation, data, and systems with Foresiet's Integrated Digital Risk Platform. 24/7/365 threat monitoring for total peace of mind.


July 10, 2025, 9 a.m.
